
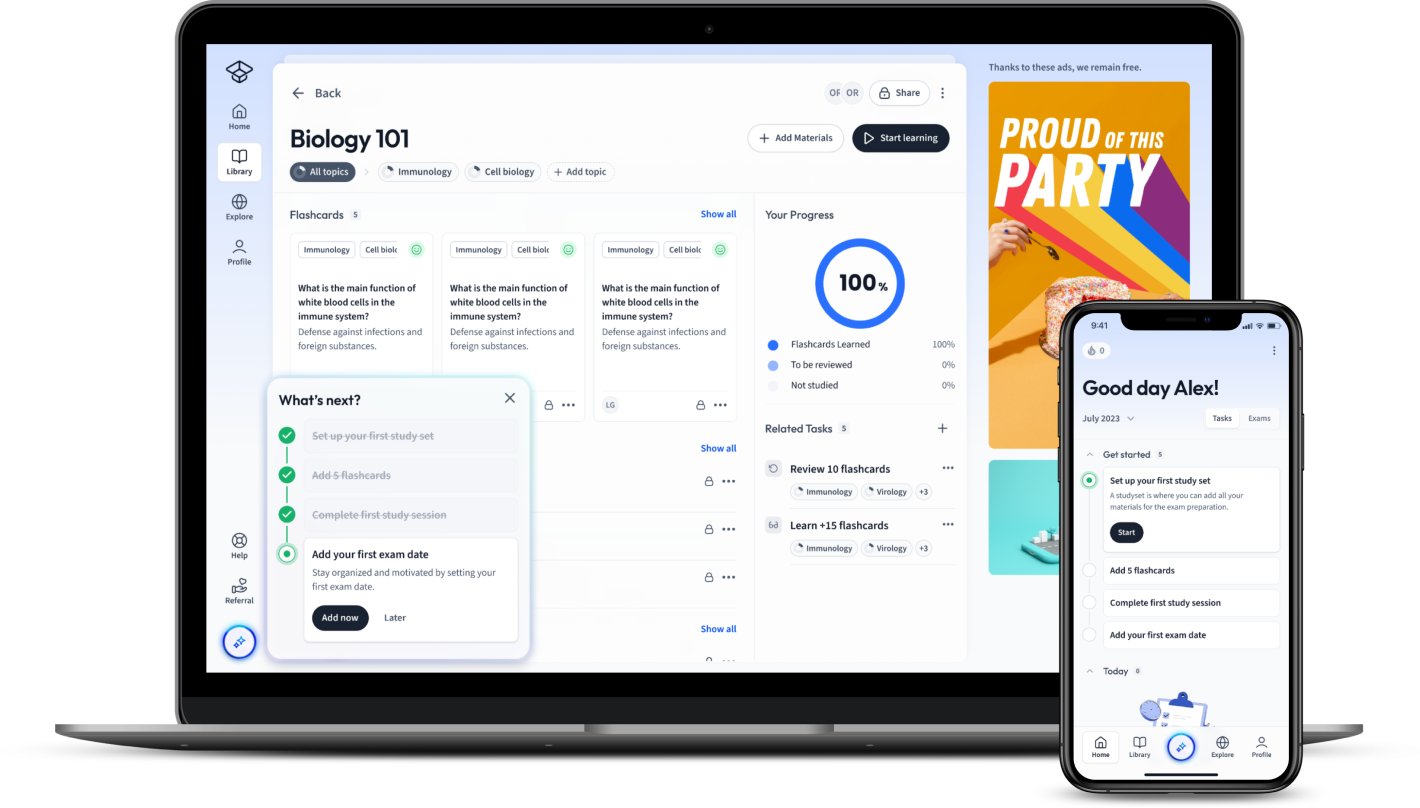
StudySmarter: Study help & AI tools
4.5 • +22k Ratings
More than 22 Million Downloads
Free
In the bustling world of corporate finance, safeguarding your business assets from potential risks is essential. This article offers an insightful look into security risk assessment, a fundamental component of business studies. You'll delve into the definition, types, applications, benefits, and the integral building blocks of security risk assessments. This comprehensive guide provides real-world examples and explains the significance of different risk assessments in maintaining a safer corporate environment. Explore this in-depth resource to understand how security risk assessment can bolster your business's security strategy.


Lerne mit deinen Freunden und bleibe auf dem richtigen Kurs mit deinen persönlichen Lernstatistiken
Jetzt kostenlos anmeldenIn the bustling world of corporate finance, safeguarding your business assets from potential risks is essential. This article offers an insightful look into security risk assessment, a fundamental component of business studies. You'll delve into the definition, types, applications, benefits, and the integral building blocks of security risk assessments. This comprehensive guide provides real-world examples and explains the significance of different risk assessments in maintaining a safer corporate environment. Explore this in-depth resource to understand how security risk assessment can bolster your business's security strategy.
In the ever-evolving corporate finance world, comprehending and mitigating potential risks is a crucial aspect. It's here that the concept of Security Risk Assessment becomes vital. Security Risk Assessment is an integral part of corporate finance, ensuring the safety of assets, providing clarity on possible threats, and empowering businesses to thrive with confidence.
Security Risk Assessment, in the context of Business Studies, is the process of identifying, analysing and evaluating potential risk factors that could compromise the security of a business. This process involves identifying vulnerabilities, potential threats, and the impact they could have on the company's operations. The goal is to anticipate and mitigate risks to keep corporate integrity intact and business operations going smoothly.
Security Risk Assessment: A systematic process of identifying, analysing, and evaluating the potential risks that could compromise the security and integrity of a business.
Here are some core areas to consider while conducting a Security Risk Assessment:
While the process seems straightforward, it is important to note that it's an ongoing process, not a one-time task.
Let's say a business operates in a country vulnerable to political unrest. A Security Risk Assessment might reveal that political instability could affect regular operations, supply chain and even physical premises of the business. Understanding this, the company could formulate contingency plans to mitigate threats, ensure business continuity, and minimise losses during such situations.
A Security Risk Assessment in Corporate Finance is a systematic approach used to understand the vulnerabilities affecting an organization's information assets, and to determine the protective measures needed to preserve the confidentiality, integrity, and accessibility of these assets.
Confidentiality: The concept of limiting information access and disclosure to authorized users—'the right people'—and preventing access by or disclosure to unauthorized ones—'the wrong people'.
Integrity: The assurance that the information is trustworthy and accurate.
Accessibility: Information is available to the authorized people when it is needed.
A set of potential risks could include:
| Types of risks |
| Hardware failure |
| Data breach |
| Malware attacks |
| Natural disasters |
Conducting a Security Risk Assessment is not just about anticipating and managing threats. It is a way for companies to gain invaluable insights into their business operations, pinpoint weaknesses and strengths, plan ahead for potential disruptions, and, ultimately, gain an edge over competitors. With its focus on securing an organisation's most vital assets, it plays a significant role in shaping an organisations' over-arching business and financial strategies.
While exploring the concept of Security Risk Assessment in Business Studies, you'll come across two main types that are often employed in businesses: Cyber Security Risk Assessment and Information Security Risk Assessment. Both kinds follow a similar approach of identifying, analysing, and mitigating risks but, their focus areas are different. They are highly intertwined, yet not interchangeable. Now, let's dive into these in more detail.
Cyber Security Risk Assessment: This type of assessment focuses on ensuring the safety of data in its electronic form. It often involves evaluating the protection measures in place to safeguard digital data from cyber threats. These threats could include hacking attempts, Distributed Denial of Service (DDoS) attacks, malware intrusions, and phishing attacks.
For instance, an online retail business may identify that customer payment information could be compromised through a cyber attack. As a result, the business might plan to employ data encryption methods and advanced firewalls to protect this sensitive data.
Information Security Risk Assessment: This assessment type is broader and encompasses the safety of data in all its forms including physical documents, verbal information, and electronic data. It evaluates how information is processed, stored, transported, and disposed of. The goal is to minimize risks associated with these activities. Threats can range from physical theft and inadvertent data loss to unsecure disposal of information.
Consider, for example, an organisation maintaining paper records of client information in their offices. An Information Security Risk Assessment would highlight the risk of these records being stolen or damaged. Mitigation strategies could include storing crucial files in a secure location or digitising these records and discarding unnecessary physical information securely.
The key difference between Cyber Security Risk Assessment and Information Security Risk Assessment lies in the scope. While Cyber Security Risk Assessment focusses purely on digital or electronic information, Information Security Risk Assessment takes a broader approach covering all forms of data – electronic, physical, and verbal.
It's crucial to note, however, these types aren't mutually exclusive. In fact, in comprehensive risk management plans, both these assessments work in tandem. An effective Information Security Risk Assessment will include a Cyber Security Risk Assessment as a vital component.
After all, with businesses becoming more digital, the boundary between physical and digital data is blurring. Thus, to protect your information assets effectively, a holistic approach encompassing both physical and digital security is critical.
In today's corporate landscape, Security Risk Assessment is applied across various industry verticals and in a number of scenarios. Let's delve into some real-world examples and discuss how different types of Security Risk Assessments are strategically implemented in businesses.
In the world of Business Studies, we look towards real-life examples to understand the functioning of concepts we study. Security Risk Assessment is an essential aspect of mitigating potential threats in a business environment. Considering this, let's examine some examples in the real world.
A first example can be found in the healthcare sector. Hospitals and healthcare institutions are known to handle extensive amounts of confidential data including patient records, medical history, financial information, and more. Given its sensitive nature, the breach of this data could have far-reaching implications both financially and ethically. Hence, conducting a regular Information Security Risk Assessment is crucial. This assessment would cover physical records, electronic data, as well as verbal communication. It would seek to ensure the data is processed, stored, shared, and discarded securely, hence minimising the potential for data breaches.
Moving over to the banking and finance sector, the focus shifts heavily towards Cyber Security Risk Assessment. Banks manage vast amounts of digital data and monetary transactions daily, making them an attractive target for cybercriminals. Here, frequent assessments would identify vulnerabilities within their IT infrastructure, digital data assets, and electronic communication channels. The resulting risk mitigation plans would put measures in place to enhance the resistance of these systems towards cyberattacks. These could include firewalls, data encryption methods, employee cyber security training, and more.
The implementation of Security Risk Assessment varies based on the type of assessment being conducted. Each type - whether Cyber Security Risk Assessment or Information Security Risk Assessment - requires a tailored approach. Let's look into the typical steps involved in each type:
Conducting Security Risk Assessments is not just procedurally necessary, but they also offer a host of advantages that support the smooth functioning and growth of businesses. The benefits range from improving data protection, enhancing compliance with regulatory standards, to fostering a safer corporate environment.
Security Risk Assessment can be defined as the systematic evaluation of an organisation's security measures to identify and analyse potential risks and threats it may face. While this is critical to any organisation's safety, Security Risk Assessments also offer a range of valuable benefits.
A deeper view into the benefits reveals that Security Risk Assessment also enhances customer trust. When customers know that businesses proactively work on their Security Risk Assessments and update their security measures, their trust in the business is reinforced. This not only aids in customer retention but also paves the way for potential new business relations.
| Better Visibility: | Security Risk Assessments provide an in-depth view of the company's current security posture. They highlight the areas within the organisation that are inadequately protected and potentially vulnerable to attacks. |
| Reduce Vulnerabilities: | Knowing the weaknesses and gaps in the security system allows the organisation to shore up its defences, minimise attack surfaces, and ensure that vulnerabilities are promptly addressed. |
| Predictive Security: | By identifying potential threats, Security Risk Assessments enable organisations to anticipate and prepare for security incidents. This provides it a critical advantage in warding off these threats. |
| Improved Recovery: | With a comprehensive risk assessment, organisations can devise strong recovery and incident response plans. This ensures minimal downtime and faster return to normal operations following an incident. |
Understanding the building blocks of Security Risk Assessment is crucial for any business aiming to enhance its risk management strategies. From recognising what entails a comprehensive assessment to the essential steps involved in conducting a successful one, let’s delve deeper into these core concepts.
The Security Risk Assessment is a crucial process that enables businesses to identify, analyse, and mitigate potential security threats. It's a preventive measure that businesses take to protect their valuable assets from the detrimental outcomes of unexpected incidents.
At the heart of this process are three important elements - threats, vulnerabilities, and impacts.
The risks associated with these elements can be calculated using this formula:
\[ Risk = Threat \times Vulnerability \times Impact \]This equation helps businesses quantify their risk exposure, which is vital for prioritising risks effectively and creating an apt mitigation strategy.
Conducting a successful Security Risk Assessment involves several critical steps. By following these diligently, businesses can ensure a thorough evaluation of their security risks.
Asset Identification: This initial step involves identifying the assets you need to protect. Assets could range from physical infrastructure and hardware to software, data, and human resources.
Threat Identification: This involves identifying potential threats that could harm or exploit your assets. A threat could be anything - a natural disaster, a network breach, hardware failure, cybercrime, or even human error.
Vulnerability Identification: This step focuses on pinpointing the vulnerabilities or weaknesses that can be exploited by potential threats. These vulnerabilities could be in your system (like weak firewalls or lack of encryption) or human-error based (like lack of awareness among employees).
Once you have identified your assets, threats, and vulnerabilities, you then proceed to assessing and calculating risks.
Risk Assessment: This involves analysing and estimating the likelihood of a threat exploiting a vulnerability and the impact it would have. This step uses the formula mentioned earlier to calculate risk.
Risk Evaluation and Prioritisation: This stage involves comparing the calculated risks and prioritising them based on their magnitude. The risks are typically divided into acceptable, tolerable, and intolerable risks.
Following risk evaluation, the next step is the formulation of a mitigation strategy.
Risk Mitigation: This requires you to develop a strategy for treating each risk. This might involve accepting the risk (if it's small and the cost to fix it is high), reducing the risk (by implementing new security measures), transferring the risk (to a third party, like cyber insurance), or avoiding the risk (by eliminating the cause).
The final step in a successful Security Risk Assessment is the continuous evaluation and repeat of the process.
Continuous Monitoring and Assessment: Risk assessment is not a one-time process. Threats and vulnerabilities evolve, and so must your risk strategies. Hence, it's essential to keep monitoring your security environment, reassessing your risks and adjusting your strategies accordingly.
Conducting a security risk assessment is not a choice, but a necessity in today's volatile and complex business environment. It's an indispensable tool for protecting your assets, driving your resilience, and ultimately, ensuring your business's survival and growth.
What is Security Risk Assessment in the context of Business Studies and how is it conducted?
Security Risk Assessment is the process of identifying, analysing and evaluating potential risks that could compromise a company's security. It involves identifying risk sources, analysing asset vulnerability, evaluating risk impact, reviewing existing security measures, and drafting risk mitigation strategies. It's an ongoing process, not just a one-time task.
What is the meaning of 'confidentiality', 'integrity', and 'accessibility' in the context of a Security Risk Assessment in Corporate Finance?
'Confidentiality' is the limitation of information access to authorized users only. 'Integrity' refers to the assurance that the information is trustworthy and accurate. 'Accessibility' means information is available to the authorized people when needed.
What are potential risks that a business could face as defined in a Security Risk Assessment?
Potential risks a business could face are hardware failure, data breaches, malware attacks, and natural disasters.
What is the focus of a Cyber Security Risk Assessment?
A Cyber Security Risk Assessment focuses on ensuring the safety of data in its electronic form. It involves evaluating protection measures in place to safeguard digital data from cyber threats.
What does an Information Security Risk Assessment encompass?
An Information Security Risk Assessment encompasses the safety of data in all its forms, including physical documents, verbal information, and electronic data. It assesses how information is processed, stored, transported, and disposed of.
What is the key difference between Cyber Security Risk Assessment and Information Security Risk Assessment?
The key difference lies in the scope. Cyber Security Risk Assessment focuses purely on digital or electronic information, while Information Security Risk Assessment takes a wider approach, covering all forms of data.
Already have an account? Log in
Open in AppThe first learning app that truly has everything you need to ace your exams in one place
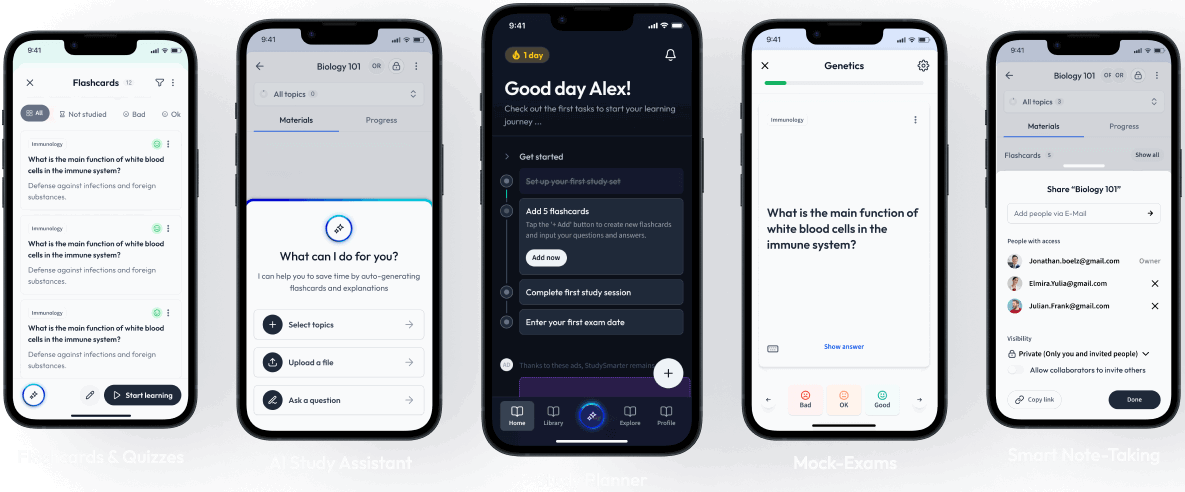
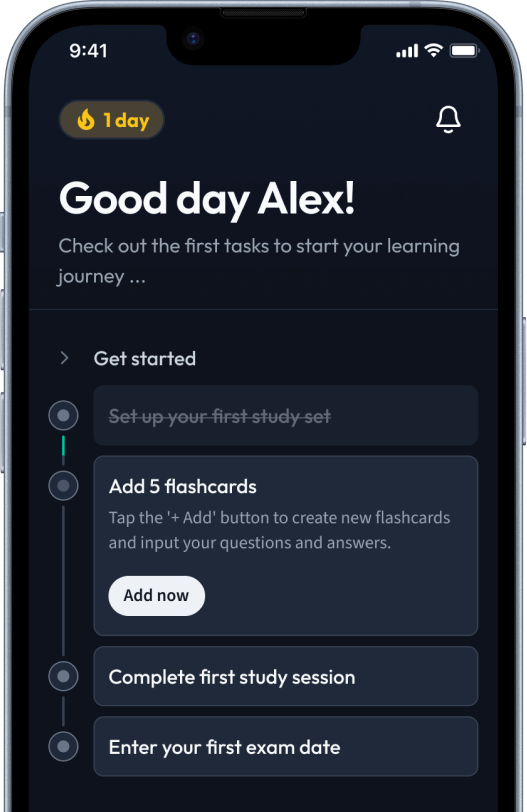
Sign up to highlight and take notes. It’s 100% free.
Save explanations to your personalised space and access them anytime, anywhere!
Sign up with Email Sign up with AppleBy signing up, you agree to the Terms and Conditions and the Privacy Policy of StudySmarter.
Already have an account? Log in